Autism spectrum disorder screening in Chinese-language preschools - Kathy Kar-man Shum, Rose Mui-fong Wong, Angel Hoe-chi Au, Terry Kit-fong Au, 2022

Mean scores on ASC-ASD subscales and overall scale for participants... | Download Scientific Diagram

Amazon.com: I'm Ready To Crush Kindergarten Monster Truck Autism ASD Long Sleeve T-Shirt : Clothing, Shoes & Jewelry
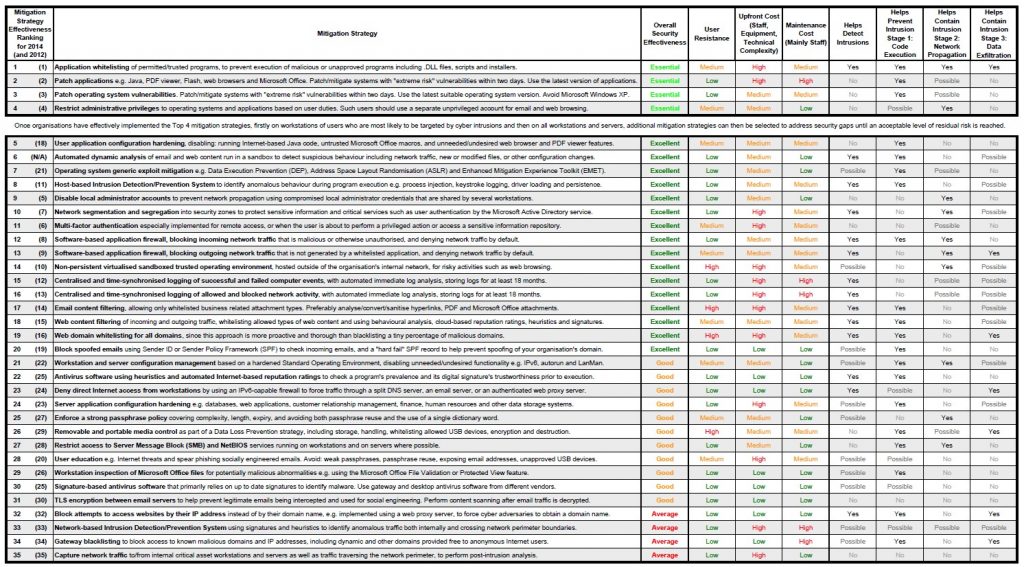
Situational Crime Prevention and the Mitigation of Cloud Computing Threats Chaz Vidal Supervisor: Raymond Choo. - ppt video online download
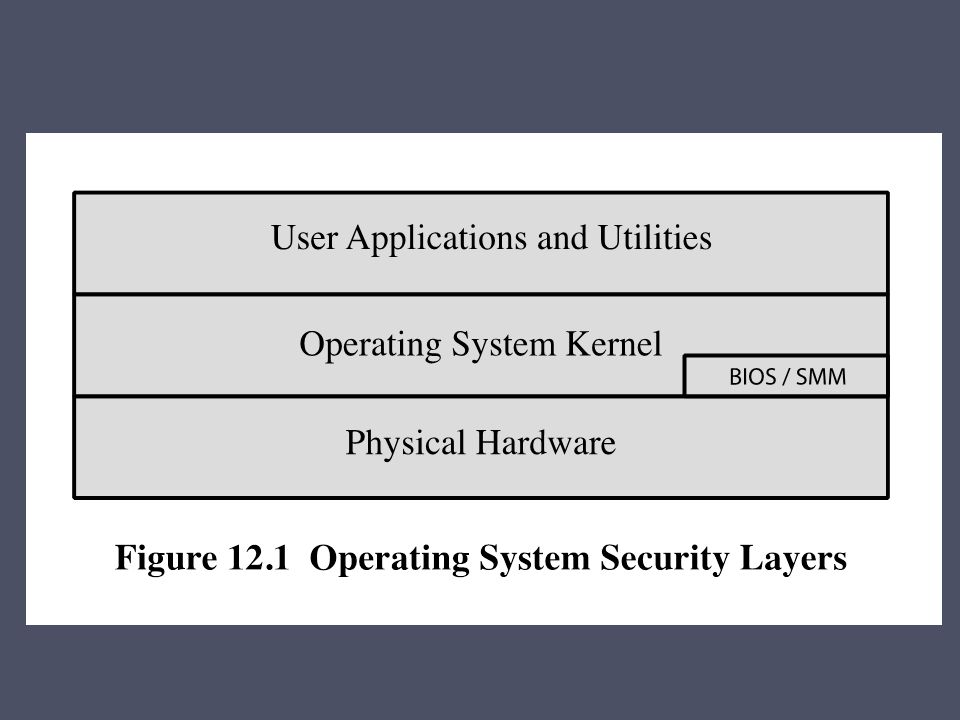
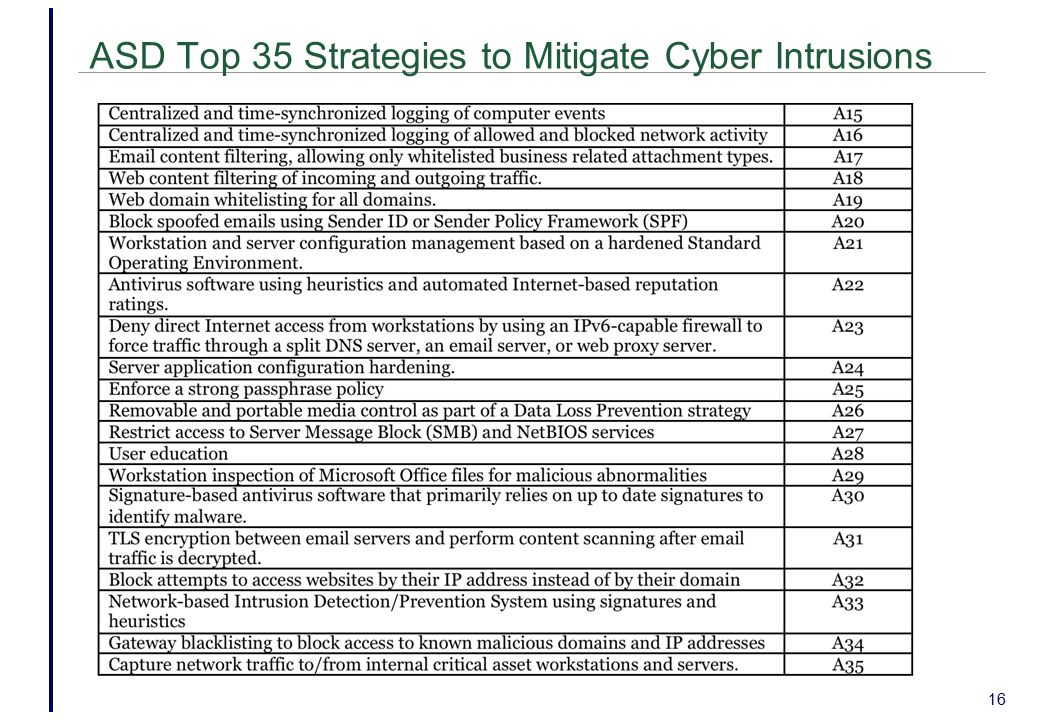
Chapter 12 Operating System Security Strategies The 2010 Australian Signals Directorate (ASD) lists the “Top 35 Mitigation Strategies” Over 85% of. - ppt download

Idiosyncratic Brain Activation Patterns Are Associated with Poor Social Comprehension in Autism | Journal of Neuroscience
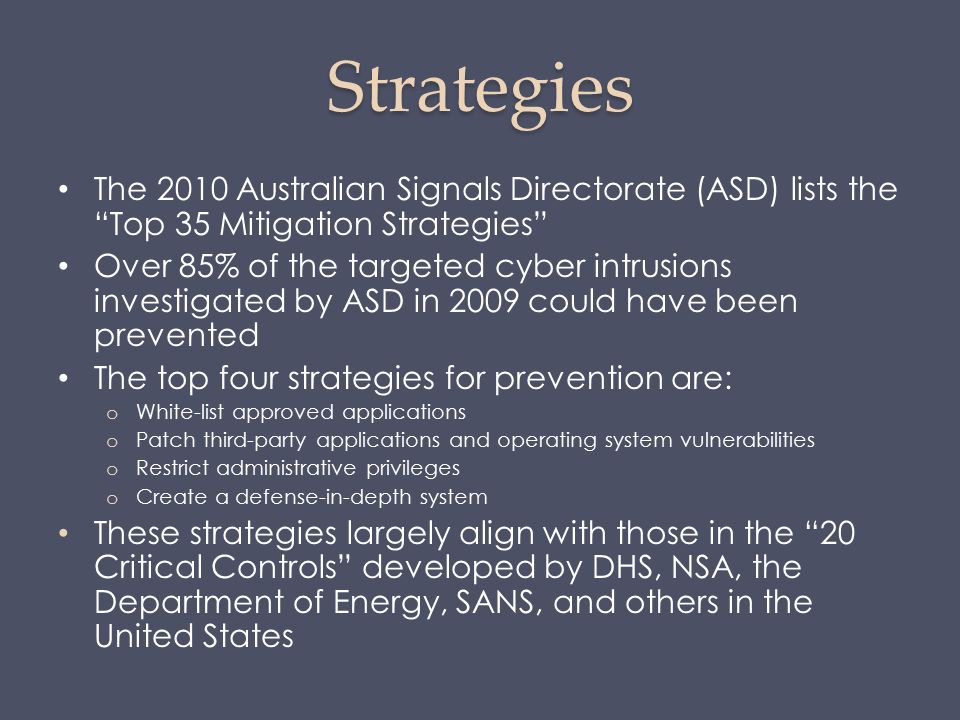
Chapter 12 Operating System Security Strategies The 2010 Australian Signals Directorate (ASD) lists the “Top 35 Mitigation Strategies” Over 85% of. - ppt download

ASD 50W LED Corn Light Bulb EX39 Removable Base, 80 Watt Equivalent 5633Lm 5000K Daylight IP64 120-277V UL-Listed, LED Post Top Retrofit Light Bulb for High Bay,Porch,Warehouse,Canopy, 6-Pack - - Amazon.com
Association between the Infant and Child Feeding Index (ICFI) and nutritional status of 6- to 35-month-old children in rural western China | PLOS ONE